Trump's Cyber Strategy: Offensive Ambitions, Defensive Gaps
By Aryamehr Fattahi | 8 March 2026
Summary
On 6 March 2026, the White House released "President Trump's Cyber Strategy for America", a 7-page document outlining 6 policy pillars and an accompanying executive order targeting transnational cybercrime. The strategy marks a decisive pivot toward offensive cyber operations and regulatory streamlining, but arrives amid deep institutional cuts to the Cybersecurity and Infrastructure Security Agency (CISA).
The central tension lies between the strategy's expansive ambitions to impose costs on adversaries and modernise federal networks, and the simultaneous reduction in the institutional capacity required to execute them. This gap between aspiration and delivery is one that adversaries are likely to test.
In the short term, the strategy is likely to energise offensive cyber planning and private-sector engagement. Over the medium to long term, however, the erosion of CISA's workforce and the delay of the Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) risk weakening baseline defences across critical sectors at a time when state-sponsored threats remain acute.
Context
On 6 March 2026, United States (US) President Donald Trump released his administration's national cyber strategy, accompanied by an executive order directing federal agencies to combat transnational cybercrime, fraud, and predatory schemes. The strategy is built around 6 policy pillars: Shaping adversary behaviour, promoting common-sense regulation, modernising and securing federal government networks, securing critical infrastructure, sustaining superiority in critical and emerging technologies, and building cyber talent and capacity.
At 7 pages, the document is notably shorter than its predecessors: the Biden administration's March 2023 strategy ran to 39 pages, and Trump's own first-term strategy of September 2018 extended to 40 pages, both with detailed objectives under each pillar. Where the Biden strategy shifted liability to software manufacturers and emphasised regulating critical infrastructure, the current document reverses that trajectory, prioritising offensive operations and deregulation. Administration officials have described the brevity as deliberate, with a detailed implementation plan to follow.
The executive order on cybercrime directs the Attorney General to prioritise prosecutions of cyber-enabled fraud and to recommend the establishment of a Victims Restoration Programme to return seized funds to victims. It designates the National Coordination Centre as the lead element for efforts against transnational criminal organisations, and directs the Secretary of State to impose sanctions, visa restrictions, and foreign assistance limits on nations that tolerate cybercrime. The White House noted that American consumers reported losing more than USD 12.5b to cyber-enabled fraud in 2024. This builds on a June 2025 executive order that streamlined Biden-era cybersecurity directives, retained core provisions on software supply chain security and post-quantum cryptography, and narrowed cyber sanctions to foreign persons only.
The strategy arrives against a threat landscape dominated by Chinese state-sponsored operations. Salt Typhoon, attributed to China's Ministry of State Security, compromised at least 9 US telecommunications companies and accessed lawful intercept systems used for court-authorised surveillance, affecting targets across more than 80 countries. As of February 2026, FBI officials assessed the threat as ongoing, with the intrusion exploiting basic vulnerabilities such as unpatched routers and weak access controls. Separately, Volt Typhoon has pre-positioned access within US critical infrastructure, including water, energy, and port systems, in apparent preparation for potential disruption during a future crisis.
Meanwhile, CISA has undergone significant upheaval. The agency has lost roughly 1,000 staff since early 2025 through buyouts, early retirements, and layoffs. The administration's fiscal year 2026 budget proposed cutting the agency's funding by nearly USD 500m and reducing its workforce from approximately 3,700 to around 2,600 positions. Key programmes were eliminated, including the Election Security Programme and Cyber Defence Education and Training. On 27 February 2026, just 1 week before the strategy's release, acting director Madhu Gottumukkala was reassigned to a different Department of Homeland Security (DHS) role after having uploaded sensitive files to ChatGPT. Nick Andersen, CISA's top cybersecurity official, stepped in as acting director, but the agency remains without a Senate-confirmed leader.
Implications and Analysis
The strategy's 6 pillars span a broad range of ambitions, from deterring adversaries to modernising federal networks and building a cyber workforce. However, there are key tensions, trade-offs, and consequences that are likely to shape its implementation and impact across government, industry, and the international landscape.
Offensive Posture versus Institutional Capacity
The strategy's defining feature is its emphasis on offensive cyber operations and its stated intent to make targeting Americans a hazardous undertaking for adversaries. It references US cyber forces' contributions to operations against Iran's nuclear infrastructure and the capture of Venezuelan leader Nicolás Maduro, signalling a willingness to publicise offensive successes as part of a broader deterrence posture.
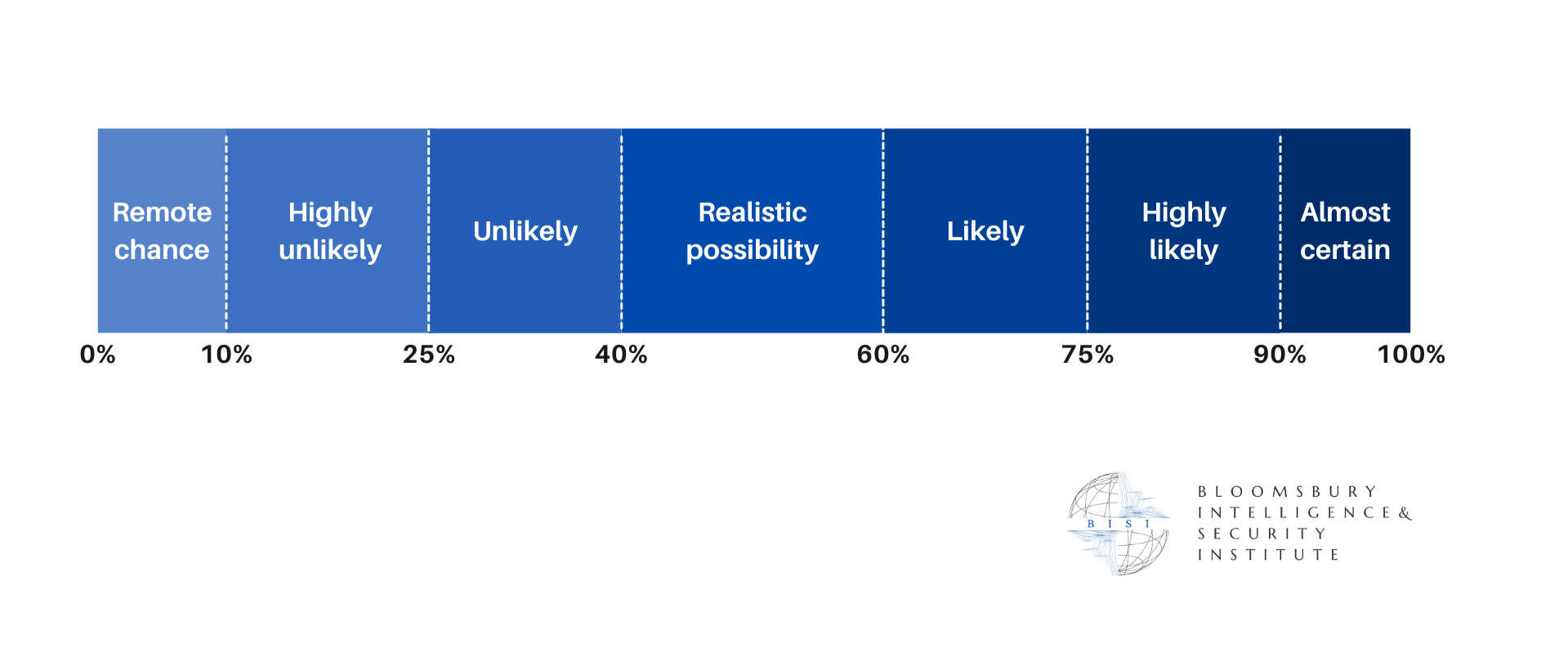
Yet the gap between this rhetoric and the state of the civilian cyber defence apparatus is stark. Offensive operations and defensive resilience are complementary rather than substitutable functions: Weakening one while strengthening the other creates an asymmetry that sophisticated adversaries can exploit. The strategy's commitment to modernising federal networks using artificial intelligence (AI)-powered cybersecurity solutions and post-quantum cryptography is credible in principle. However, the agency most responsible for coordinating federal network defence and critical infrastructure protection has lost a third of its staff, has seen its National Risk Management Centre targeted for a 73% budget reduction, and operates without confirmed leadership. There is a realistic possibility that the gap between strategic intent and institutional capacity will widen before it narrows, particularly if congressional efforts to restore CISA funding are only partially successful.
The Threat Landscape and Deterrence Calculus
The strategy's framing of adversary behaviour as the primary target of US cyber policy is well-aligned with the threat environment, but the policy instruments chosen may be better suited to some threats than others. Salt Typhoon and Volt Typhoon represent fundamentally different challenges. Salt Typhoon is a large-scale espionage operation; the intelligence value to Beijing is immediate and ongoing, making deterrence through offensive signalling inherently difficult. Volt Typhoon, by contrast, represents pre-positioned capability held in reserve for a potential crisis, where a credible deterrent posture could influence Chinese decision-making about whether to activate that access.
The strategy does not distinguish between these 2 threat types, instead grouping them under a broad mandate to impose costs. This risks conflating espionage, which all major powers conduct and which is extraordinarily difficult to deter, with preparation for destructive attacks, where deterrence has a stronger theoretical foundation. An undifferentiated offensive posture also carries escalation risks. In an environment where tensions over Taiwan, trade, and technology competition remain elevated, expanded US cyber operations are likely to prompt adversary responses that the diminished defensive apparatus is less equipped to absorb. Cyber actors, already active against US targets, will likely recalibrate their operations in response to the strategy's confrontational tone, particularly given ongoing geopolitical frictions and conflicts like the current Iranian strikes.
Regulatory Streamlining and Critical Infrastructure
The common-sense regulation pillar reflects the administration's broader deregulatory agenda and has drawn support from industry stakeholders who viewed Biden-era expansions of cyber regulation as burdensome. The administration has delayed finalisation of the CIRCIA rules from the original October 2025 deadline to May 2026, with sector-specific town halls scheduled throughout March 2026. The strategy also includes cryptocurrency and blockchain among systems to be secured, aligning with the administration's broader digital asset priorities but raising questions about resourcing amid reduced civilian cyber capacity.
For critical infrastructure operators, the implications are mixed. Reduced regulatory burden may accelerate innovation and investment in some sectors. However, the absence of a finalised mandatory incident reporting framework for critical infrastructure coincides with the period of greatest threat from state-sponsored actors. The rescission in November 2025 of Federal Communications Commission rules introduced after the Salt Typhoon compromise further reduced the regulatory tools available to compel telecommunications providers to address known vulnerabilities. Experts have assessed that the Salt Typhoon intrusion has not been fully remediated from telecommunications networks and that basic cybersecurity failures enabled the breach. Without regulatory mechanisms to enforce baseline security standards, there is a realistic possibility that the voluntary, collaborative approach favoured by the strategy will prove insufficient to drive the investment required to harden networks that are actively under threat.
Private-Sector Engagement and Legal Uncertainty
The strategy's call to unleash the private sector by creating incentives to identify and disrupt adversary networks represents a significant conceptual shift. Several US technology companies voiced support for the administration's stated goal of deeper industry partnership. However, the operational and legal implications of incentivising private-sector disruption of adversary networks are substantial. Questions of corporate liability, rules of engagement, and coordination with government offensive operations remain unaddressed in the strategy document. Without clear legal frameworks, there is a risk that private-sector actors either overreach, potentially triggering international incidents, or remain cautious, rendering the pillar aspirational.
The erosion of CISA's stakeholder engagement capabilities compounds this challenge. The proposed budget targeted the Stakeholder Engagement Division and the Joint Cyber Defence Collaborative, which convened major technology providers for threat coordination. The infrastructure for public-private collaboration has been weakened at the moment the strategy demands its expansion.
Workforce, Talent, and Morale
The cyber talent pillar sits uncomfortably alongside the reality of mass departures from CISA and the proposed elimination of the Cyber Defence Education and Training programme. The strategy acknowledges the importance of building cyber capacity but offers no details on how this will be achieved while the federal government's primary cyber training apparatus is being dismantled. Former officials have described staff morale at CISA as deeply damaged, and the broader federal cyber workforce is likely to find the private sector increasingly attractive by comparison. For government agencies already struggling to compete for cyber talent, the signal sent by these cuts is likely to compound existing recruitment challenges. This dynamic is unlikely to reverse without sustained investment and a demonstrable commitment to valuing cyber defence careers in government.
Allied Confidence and Adversary Perceptions
The strategy's language on countering authoritarian technologies and working with allies who share democratic values signals continuity with longstanding US cyber diplomacy. However, allied confidence in US cyber leadership has been tested by the administration's domestic actions. Cuts to CISA, the elimination of election security programmes, and repeated leadership turnover send mixed signals to partners who rely on US cyber capacity for collective defence. European and Indo-Pacific allies are likely to hedge by accelerating their own sovereign cyber capabilities, a trend already underway through initiatives such as the European Union's Cyber Blueprint.
For adversaries, the strategy's aggressive rhetoric is almost certainly being weighed against the observable reduction in US defensive capacity. Cyber planners are likely to assess that the current period offers a window of relative advantage for sustained espionage and pre-positioning operations. The strategy's normative language on countering surveillance states also introduces a tension that adversaries are likely to exploit. Critics have noted how the contradiction between this stance and domestic surveillance concerns under the current administration is a vulnerability in the credibility of US cyber diplomacy that Beijing and Moscow are likely to leverage in multilateral settings.
Forecast
Short-term (Now - 3 months)
The Office of the National Cyber Director is likely to begin drafting implementation plans for each pillar. CISA's leadership transition under acting director Andersen is likely to stabilise operations, but morale and staffing challenges will almost certainly persist. Finalisation of the CIRCIA rule by May 2026 remains uncertain, and further delay is a realistic possibility.
Medium-term (3 - 12 months)
Congressional appropriations battles will likely result in a CISA funding level between the administration's proposed cuts and the Senate's more moderate reductions, but the agency is unlikely to recover pre-2025 capacity. There is a realistic possibility that a significant cyber incident targeting US critical infrastructure will expose the gap between the strategy's ambitions and diminished response capacity, potentially forcing a policy correction.
Long-term (>1 year)
The strategy's offensive orientation is likely to produce visible deterrence actions against cybercriminal and state-sponsored groups. However, unless defensive investment is restored, the US is highly likely to face an increasingly asymmetric posture where offensive capability outpaces defensive resilience. The federal cyber workforce pipeline is highly likely to narrow, with consequences extending well beyond the current administration.