Defence Technology in an Integrated Battlespace: How Autonomy is Reshaping Modern Warfare.
By Charlotte Voss | 2 March 2026
BISI is proud to present this piece in collaboration with CyberWomen Groups CIC. Through this partnership, we have combined our expertise in political risk with their knowledge of cyber security to deliver a fresh perspective on emerging threats.
CyberWomen Groups CIC is a student-led initiative dedicated to diversifying STEM by supporting and connecting university students interested in or studying cybersecurity, regardless of gender identity.
Summary
The rapid integration of autonomous and automated systems into military operations is transforming force capability, accelerating decision‑making, and reducing direct human exposure to harm.
Increased reliance on interconnected, globally sourced defence technologies expands the cyber attack surface, creating new vulnerabilities and offering threat actors more opportunities for covert, low‑visibility disruption across supply chains and operational systems.
As militaries move toward a persistent, technology‑driven operational environment, defence organisations will face mounting pressure to strengthen resilience, anticipate emerging attack vectors, and adapt doctrine, procurement, and preparedness to the realities of automated warfare.
Context
Defence technology has undergone a radical transformation with the convergence of cyber and physical systems. As the global economy accelerates investment into autonomous platforms and Artificial Intelligence (AI) led decision tools, cyber operations are no longer considered peripheral factors and instead sit at the core of modern warfare. Understanding this shift is necessary in order to better anticipate and prepare for future threats, whilst also providing new and intriguing operational advantages.
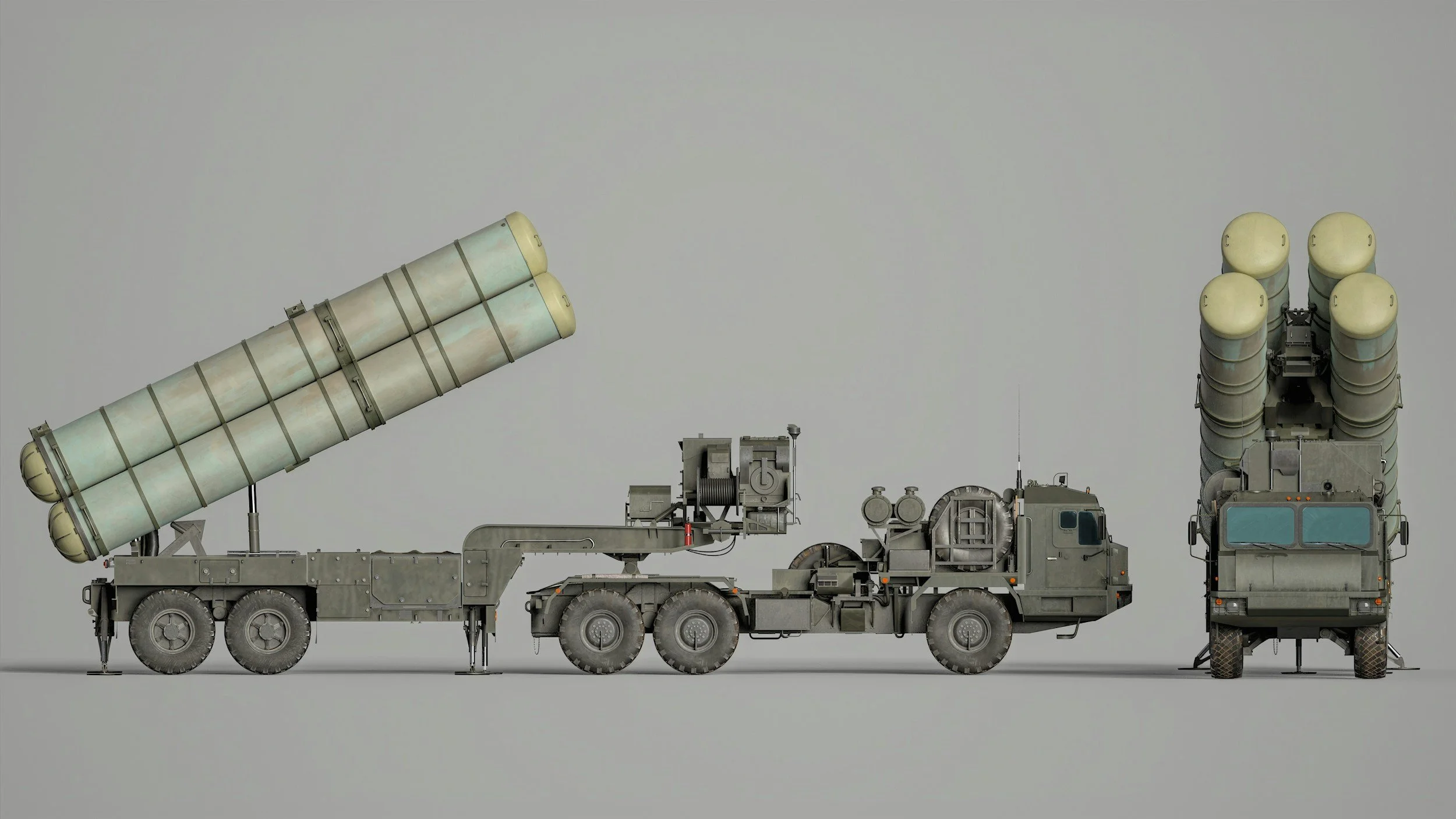
Cyber-physical integration now underpins military capability, as digital and physical systems become increasingly intertwined. Modern military operations increasingly rely on autonomous platforms and AI-enabled battlefield management systems. Such technologies enable accelerated decision-making and enhanced situational awareness, whilst limiting the need for direct human exposure to physical harm. AI systems can support intelligence analysis, logistics optimisation and target identification on the battlefield, enabling coordinated and accelerated defence action across multiple domains.
However, by integrating autonomy into combat and defence systems, both the frequency and potential impact of cyberattacks increase exponentially. Autonomous systems depend on software security, reliability and integrity, all of which can be targeted by adversaries often remotely. If a drone or an AI-enabled command system is compromised, there is a possibility that this could allow threat actors to redirect these technologies and derail strategic procedures or cause catastrophic destruction if escalated. With the expansion and integration of military defence tools, it is paramount that secure command-and-control links are prioritised.
Cyber Vulnerabilities in Military Supply Chains
In addition to frontline systems, the resilience of defence supply chains has emerged as a strategic vulnerability. Since modern military tools require complex hardware, defence engineers depend on complex global networks of suppliers, logistics providers and software developers to develop and produce them. This creates many opportunities for cyber sabotage through means of malicious code insertion, tampering with firmware, or disrupting transportation and maintenance processes. The complexity of these supply chains also makes it increasingly difficult to detect or prevent manipulation at any stage, and many intrusions may remain undetected whilst compromising reliability. States now not only have to protect their domestic defence industries, but also regulate the security of foreign subcontractors or suppliers, which is difficult to monitor.
Recent incidents, including the compromise of semiconductor manufacturers and other targeted attacks on defence logistics software, highlight how supply chains serve as highly effective targets despite often being indirect. Supply chain infiltration can be considered a low-visibility way of inflicting high-impact disruption, so to strengthen resilience, it is crucial to apply zero trust architectures, monitor processes, and maintain communication between government, production and intelligence sectors.
These shifts in the defence sector are driving the evolution and reshaping of cyber warfare doctrines. Offensive cyber tools allow states to reduce enemy communications, manipulate data, and interfere with surveillance systems and critical infrastructure. Meanwhile, defensive doctrine places more of an emphasis on persistence and threat intelligence within military networks. Recent recognition of cyberspace as a ‘continuous battleground’ blurs traditional distinctions between being in states of ‘peace’ or ‘conflict’. The battlespace now extends far beyond open conflict, with states engaging in constant competition to have access to and control over each other, both physically and digitally.
Strategic Implications of Autonomous Integration
Ultimately, defence technology is increasingly being defined by autonomy, given the growing integration of cyber and physical elements. Although autonomy and AI powered systems provide significant advantages, they also present many risks and new exploitable targets. Defence effectiveness will thereby depend on a combination of technological innovation, but also the security of supply chains, cyber resilience, and the globe’s ability to adapt doctrine to a security environment defined by speed, complexity, and continuous competition.
Forecast
Short-term (Now - 3 months)
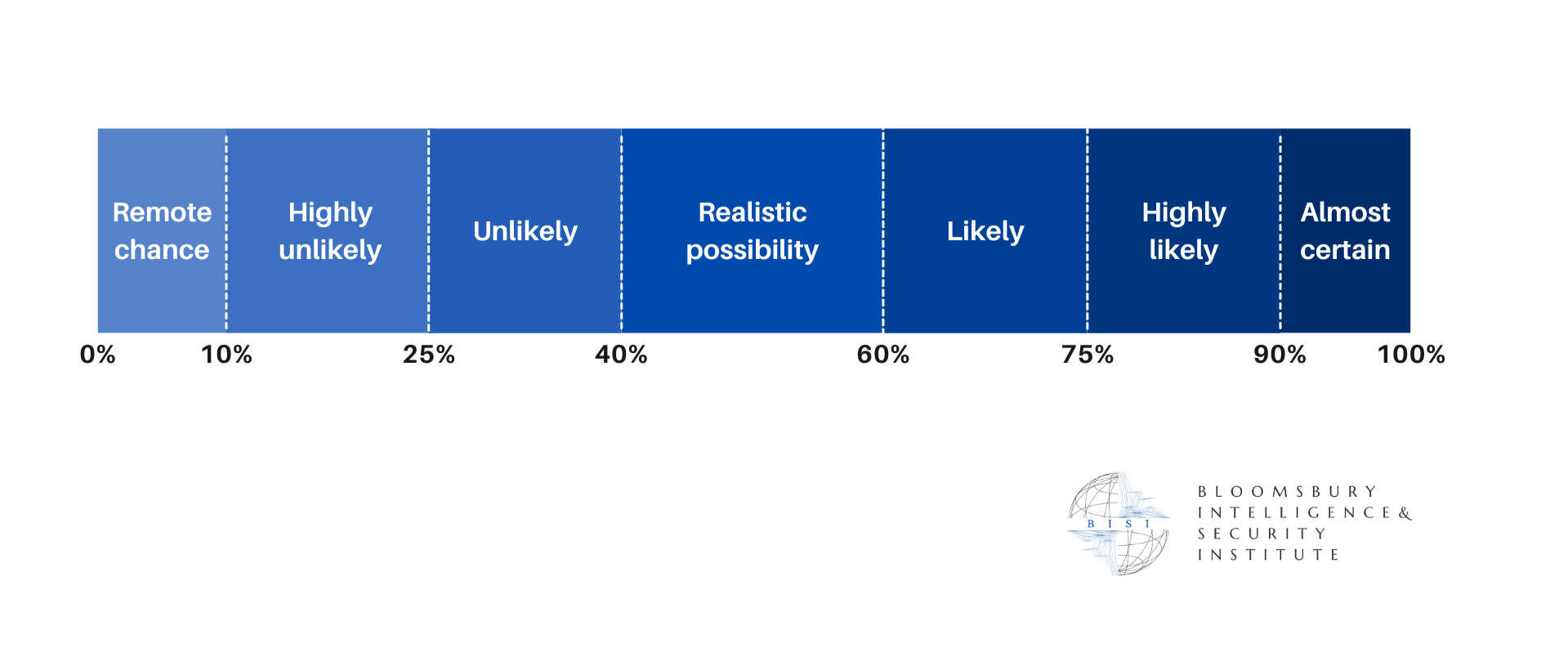
Deployment of autonomous platforms across military networks is set to likely accelerate, driven by geopolitical tension and the need for faster decision‑making in volatile environments. As cyber integration deepens in parallel, more threat actors are likely to probe complex defence supply chains for opportunities to disrupt development and operational readiness.
Medium-term (3 - 12 months)
Growing awareness of supply‑chain exposure will likely prompt tighter security, more rigorous surveillance of procurement processes, and a shift toward sourcing critical components locally where feasible. These adjustments can likely begin to reshape global hardware dependencies and introduce new patterns of strategic competition among defence producers.
Long-term (>1 year)
Enhanced cyber‑physical integration will likely reinforce emerging models of persistent, below‑threshold competition, as states race to field increasingly efficient autonomous systems. This dynamic is likely to entrench a global security environment characterised by heightened strategic pressure.