Assessing Quantum’s Risk on Critical Infrastructure
By Autumn Bamford | 2 March 2026
BISI is proud to present this piece in collaboration with CyberWomen Groups CIC. Through this partnership, we have combined our expertise in political risk with their knowledge of cyber security to deliver a fresh perspective on emerging threats.
CyberWomen Groups CIC is a student-led initiative dedicated to diversifying STEM by supporting and connecting university students interested in or studying cybersecurity, regardless of gender identity.
Summary
While the quantum computing threat to cryptography is acknowledged, current discussions focus primarily on information technology, overlooking potentially greater risks to critical infrastructure systems that rely on operational technology.
Vulnerabilities lie in critical infrastructure that uses RSA, in the integration of PQC into resource-constrained systems, and in service continuity.
Without proactive assessment, migration strategies, and quantum-aware security planning, critical infrastructure will remain vulnerable to high-impact quantum-enabled attacks in the long term; therefore, early preparation is essential.
Context
The threat quantum computing poses to modern cryptography is recognised by the UK government, yet discussions surrounding this risk remain focused on information technology (IT) security. While compromised data and digital communications are a serious concern, this emphasis overlooks a potentially greater threat: the security of critical infrastructure. Critical infrastructure relies on operational technology (OT) systems, whose failures can cause physical damage, service disruption, and risks to human safety. Historically, OT environments benefited from internet isolation and proprietary protocols, but increasing connectivity has significantly expanded their attack surface. Consequently, OT systems now face many of the same cyber threats as IT systems, often without equivalent security maturity, making them vulnerable to future quantum-enabled attacks. A large-scale attack could also have economic consequences, disrupting markets, supply chains, and industrial productivity both locally and globally.
Current critical infrastructure may have been in service for decades, meaning cryptographic decisions made in the past are unchangeable. Due to their age and design, many systems use RSA encryption. However, RSA encryption is a primary target of quantum attacks, as Shor’s algorithm provides a means of breaking it. A specific example where this might cause issues is in OT devices that rely on RSA-based digital signatures for firmware updates and secure boot: adversaries could forge these signatures, enabling unauthorised firmware installation and, subsequently, the spread of malware or backdoors.
This situation creates significant technical, strategic, and operational challenges for critical infrastructure operators. To protect against these threats, critical infrastructure would need to implement post-quantum cryptography (PQC). This creates a significant challenge when considering OT systems, which are resource-constrained, have long operational lifespans, and cannot be easily patched or replaced. PQC algorithms often require greater computational resources and increased overhead; integrating PQC into systems without disrupting real-time performance or safety-critical operations is a complex, expensive task.
Implications
Beyond the technical challenges of implementing PQC, quantum computing introduces significant strategic and operational risks for critical infrastructure operators. One of the most pressing concerns is the “harvest now, decrypt later” threat, in which adversaries collect encrypted OT communications today with the intention of decrypting them once quantum capabilities mature. This could expose sensitive data, network architectures, and control logic that remain relevant for long periods due to system longevity. Such exposure would significantly reduce the effort required for future attacks and increase the likelihood of successful exploitation.
Ultimately, the quantum threat to critical infrastructure should be treated as a long-term, high-impact risk rather than a purely theoretical concern. While large-scale quantum computers capable of breaking RSA are not yet operational, the time required to design, test, certify, and deploy cryptographic changes in critical infrastructure systems means that preparation must begin well in advance. Disruption to critical services such as water treatment plants, transportation networks, or energy distribution could hugely impact the lives of millions. Such disruptions would also impose high economic costs and could exacerbate social inequalities by disproportionately affecting vulnerable populations. Therefore, proactive assessment, migration strategies, and quantum-aware security planning are essential to ensuring the resilience, safety, and continuity of critical infrastructure in a post-quantum world.
Forecast
Short-term (Now - 3 months)
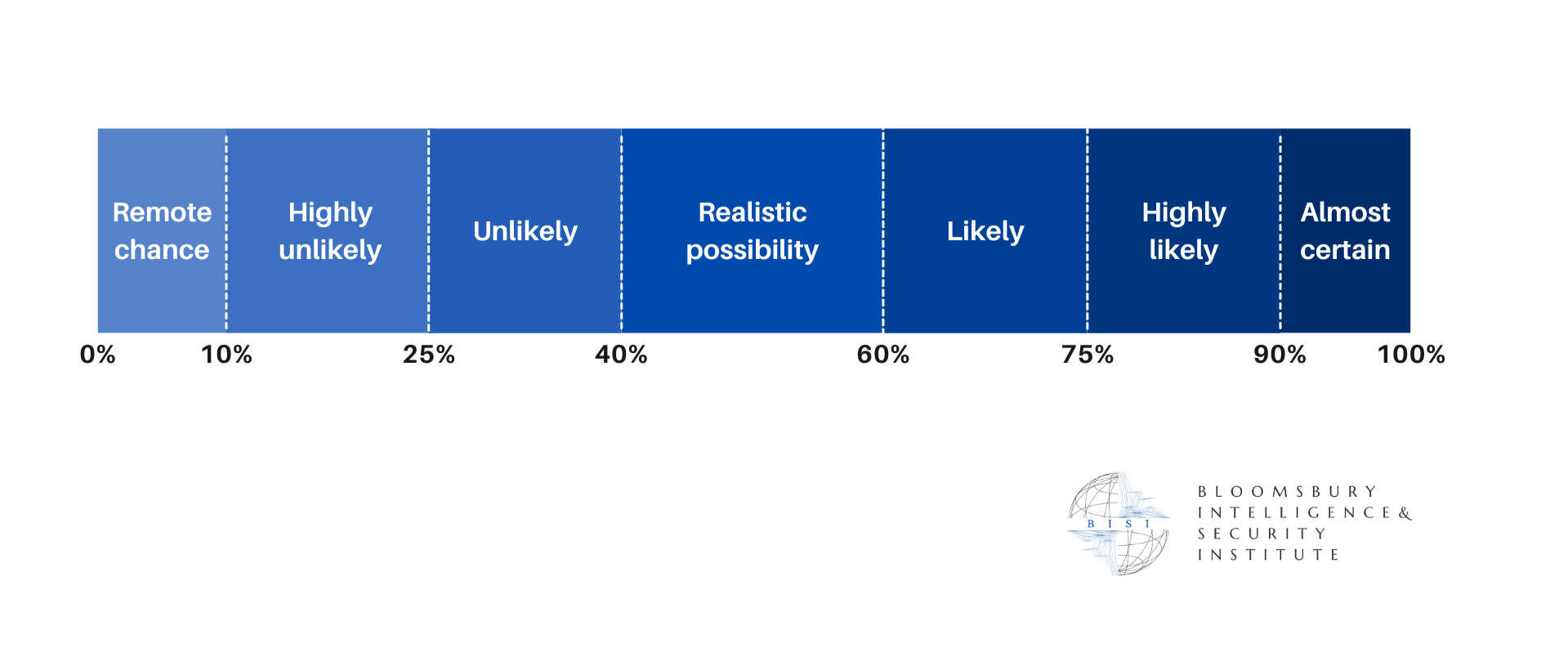
Given the current progress of quantum computing, it's highly unlikely that any quantum based attacks would be carried out on a critical infrastructure or OT systems. This forecast would change only if there were an unexpected breakthrough in quantum computing. However, such a rapid advancement is currently unlikely due to the technical, financial, and scientific barriers involved.
Medium-term (3 - 12 months)
As quantum threats aren't predicted to be implemented until 2030, quantum attacks against critical infrastructure remain unlikely, though they will increase in probability. This, too, will only change if there is a major development made in research or if government funding for projects increases.
Long-term (>1 year)
Once relevant quantum technology becomes more widely accessible, it is highly likely that critical infrastructure will be targeted first, given its importance to national stability and its clear vulnerabilities to quantum attacks. This likelihood would only decrease if the suggested steps were made, such as PQC migration being widely implemented and legacy systems are either redesigned or retired. It remains unlikely that early quantum attacks would occur outside of a state-level attack.