Cybersecurity Vulnerabilities in North American Satellite Ground Segments
By Ana Moroșanu | 23 February 2026
BISI is proud to present this piece in collaboration with CyberWomen Groups CIC. Through this partnership, we have combined our expertise in political risk with their knowledge of cyber security to deliver a fresh perspective on emerging threats.
CyberWomen Groups CIC is a student-led initiative dedicated to diversifying STEM by supporting and connecting university students interested in or studying cybersecurity, regardless of gender identity.
NASA/Wikimedia
Summary
Systemic flaws in North American ground stations, particularly unpatched legacy software and Commercial Off-the-Shelf (COTS) hardware, provide Tier 5 and 6 actors with viable attack vectors.
Exploitation of command-and-control links poses a High-severity risk to orbital safety and could trigger significant volatility in global financial markets.
The deteriorating threat landscape is driving a surge in private capital toward 'secure-by-design' systems and collaborative frameworks like the Colorado-based Space ISAC.
Context
The ground segment, as a primary strategic chokepoint, often represents the most accessible path to compromising an entire satellite constellation. North American infrastructure is increasingly exposed as satellite populations have grown, with many relying on interconnected terrestrial networks. For example, since 2020, providers such asEchostar have launched over 8,000 low-earth orbit (LEO) satellites.
As a result, two primary threat categories emerge: Tier 6 state actors possess the resources for high-impact operations, evidenced by the 2022 Viasat disruption. Notably, that attack exploited unpatched Fortinet VPN vulnerabilities in the ground infrastructure rather than in the satellites themselves, underscoring the risk posed by terrestrial entry points. Meanwhile, Tier 5 criminal syndicates target commercial operators for ransom payments. The transition to commercial-off-the-shelf (COTS) hardware simplifies these efforts, thereby enabling adversaries to map vulnerabilities through open-source research and standard digital tools.
Implications
A breach of North American ground control will almost certainly compromise government legitimacy and erode trust in critical services, especially since satellite outages have often sparked social unrest. Such disruptions have the potential to create information voids that state-sponsored actors can then exploit via disinformation campaigns to manipulate public opinion during geopolitical crises.
The core operational vulnerability is focused on “mission integrity”. Compromising the Command and Data Handling Subsystem (C&DHS) allows an attacker to seize the 'brain' of the satellite. This, in turn, enables the unauthorised modification of orbits or total payload deactivation. Additionally, 'data spoofing' remains a critical risk; by feeding false telemetry to a ground station, attackers can trick operators into executing manoeuvres that lead to the permanent loss of the asset.
A lack of unified international regulations creates a persistent security gap. While the FAA-led North American aviation industry is currently undergoing a mandatory 'digital modernisation' to close infrastructure gaps, the space sector still lacks these enforced safety standards. This environment attracts Tier 6 actors intent on exfiltrating proprietary aerospace technology or gaining a strategic military advantage.
Disrupting GNSS (GPS) timing signals would likely trigger 'flash crashes' in financial markets, yet the risk environment is also birthing a multibillion-dollar industry. We observe record levels of private investment entering the 'secure-by-design' market, with the global space cybersecurity sector projected to reach USD 5.2b (GBP 4b) by the end of 2026. The expansion of the Space ISAC in Colorado Springs confirms that commercial entities are now prioritising collaborative defence to protect assets valued at billions of dollars.
Forecast
Short-term (Now - 3 months)
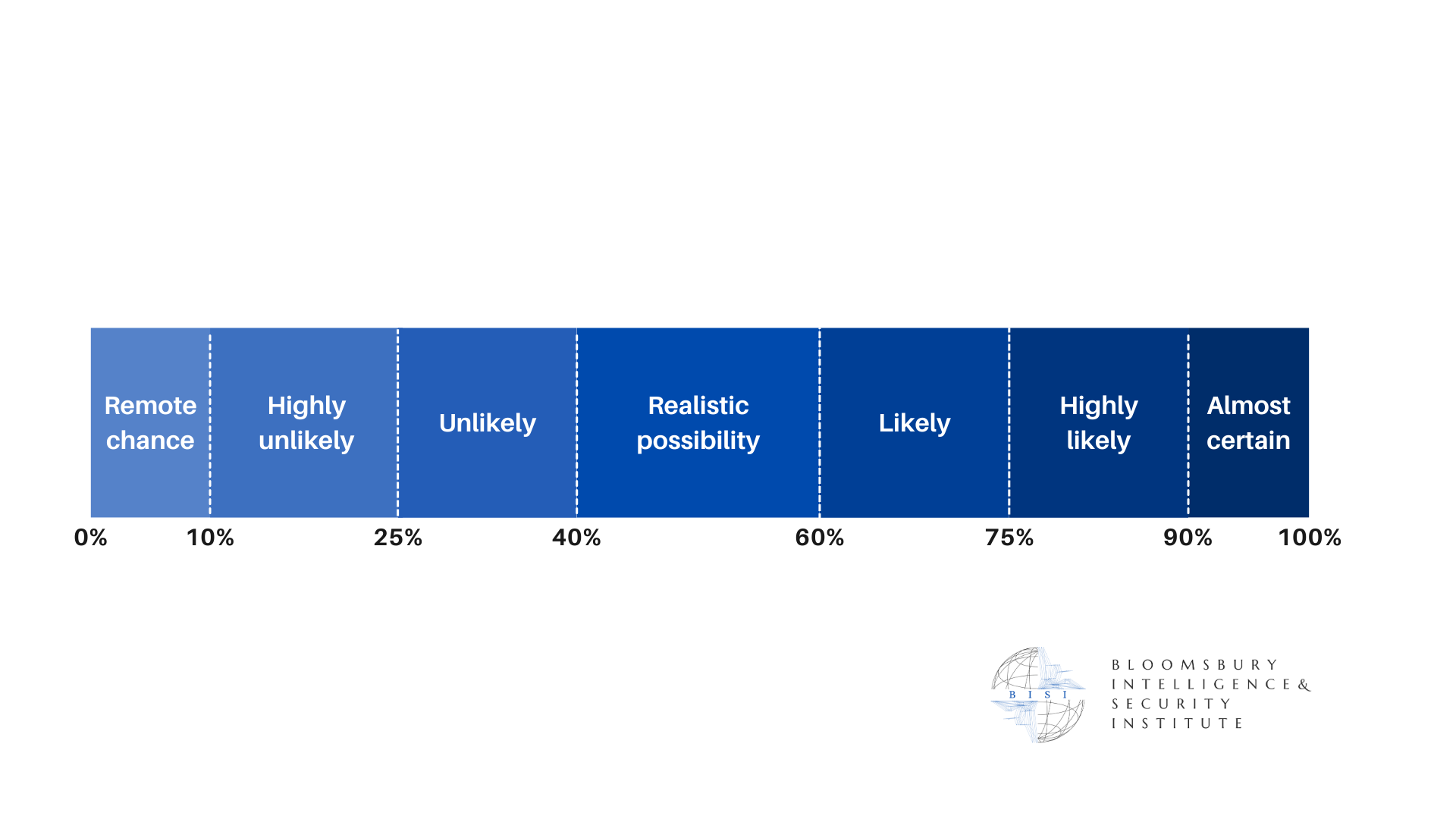
It is likely that Tier 5 cybercriminals will target a small North American commercial ground station with ransomware. These incidents typically result in data leaks rather than a loss of satellite control.
Medium-term (3 - 12 months)
There is a realistic possibility that state-backed actors will exploit unpatched VPNs in North American ground stations for espionage. This poses a high risk due to the potential theft of classified aerospace schematics.
Long-term (>1 year)
It is highly likely that the absence of global space regulations will result in a major systemic failure by 2027. An attack on precision timing signals would likely cause severe instability across global financial sectors.